Provides optimal security tailored to usage scenarios
TIGEREYE SECURITY SOLUTION provides an authentication function that allows you to change the security strength by switching settings according to your operational style and security level.
TIGEREYE SECURITY SOLUTION combines multiple security factors in real time and scores authentication results numerically to provide optimal security for each usage scenario. The recognition rate in actual use is higher than the usual AI recognition rate (affected by distance, brightness, angle of reflection, etc.). Based on the service's operation, the customer can configure the settings as desired.
Flexible security settings for both convenience and security
Traditionally, the search for strong security has generally come at the expense of convenience, but with TIGEREYE SECURITY SOLUTION, you can customise security layers, security rules and scoring factors (in three categories) to choose the best security measures. The system can be customised with security layers, security rules and scoring factors (in three categories). For example, you can set up the system to suit your operation and situation, for example, using simple facial recognition for situations where staff are nearby, and conversely introducing technology to prevent photo image spoofing, two-stage authentication or an approval process by an administrator for situations where there is no third-party supervision. Furthermore, it is possible to determine whether authentication is possible or not according to the quality of the image and maintain a high recognition rate.
-

Fraud prevention and crime deterrence when authenticating a person in a completely unattended environment
-

Self-authentication by users themselves to prevent spoofing and fraud
-
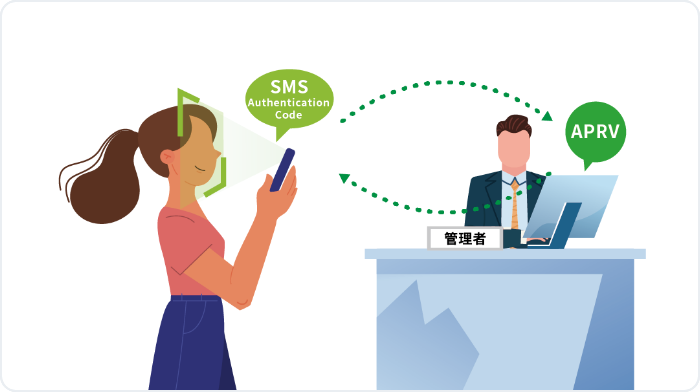
Third-party authentication by an administrator, such as requesting an authorization code or requesting authorization
Dynamic Schedule
You can freely set your own schedule, such as increasing the authentication intensity at night, on weekends, and during unattended hours.
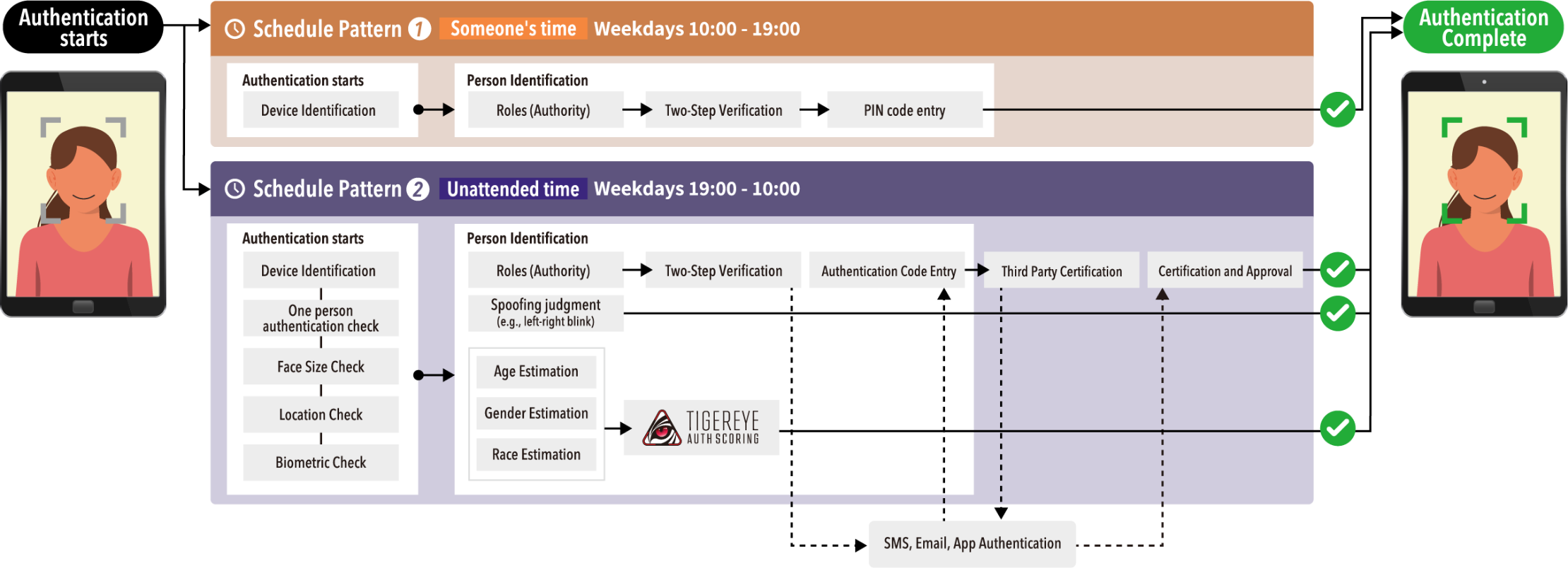
For example, the system can be configured to suit the operation and scene, such as using simple facial recognition to authenticate when staff are in close proximity, and conversely, introducing technology to prevent photo image spoofing, two-step authentication, or an approval process by a manager when there is no third-party supervision. Furthermore, the system can determine whether authentication is possible or not based on the quality of the image and maintain a high recognition rate.
Based on the service side operation, more than 600 security settings can be configured for 25 items to increase robustness. More security items will be added in the future.

TIGEREYE REALTIME ACTIVE LIVENESS DETECTION
Prevent fraudulent authentication with still images (photo images).
TIGEREYE REALTIME ANTI_MISRECOGNITION
Implemented features to increase recognition rates, and settings can be toggled to enhance the required level of security.
TIGEREYE MFA
Multi-factor authentication including two-step authentication with authentication code, authentication authorization with administrator approval, SMS/EMAIL/third-party authentication (administrator), and 3rd authentication application (Authenticator)
TIGEREYE AUTH SCORING
Real-time credit scoring based on multi-factor identification decisions.CASE
We provide advanced authentication functions for various situations, such as access control according to the security level of each location and strict prevention of impersonation in university entrance examinations.
-
Case.1 Office
As access control on weekends and holidays when the company is closed.When a person's face is recognized at the entrance of the office, the manager is notified and can know who is in the office. Or, only those who have been authorized by the manager can enter the office.
-
Case.2 University
As a reliable method of identification for entrance examinations, regular tests, etc.Entering by facial recognition and linking seat numbers with facial information to identify those who are present and those who are absent. Also, by recording when people leave the room, those who have no record of their entry can be detected.
As admission to places that are only available to certain students, such as laboratories, medicine rooms, and forbidden book areas.Facial recognition should trigger a notification to the administrator.
-

Case.3 Hospital
As access control to areas where only a limited number of people are allowed to enter.Notifies the administrator when facial recognition is performed.
-

Case.4 Condominiums
For entrance control.Not only residents, but also visitors such as courier companies can unlock the door with facial recognition. Temporary visitors can be notified to the manager.
Functions
| product | KAOPASS QR | KAOPASS Attendance | KAOPASS Key & Entry/Exit | KAOPASS Auth | KAOPASS Pay | KAOPASS Ticket | KAOPASS Table Order | KAOPASS Register | ||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Always Authenticated | Authentication Each Time | Authentication at each time of imprinting | Unlocked at any time | Authentication at any time | NW Camera (TIGEREYEBOX) |
Authentication at each time | Authentication at each time | Unlocked at any time | Authentication at any time | NW Camera (TIGEREYEBOX gate interlocked) |
Unlocked at any time | Unlocked at any time | Authentication at any time | |
| Anti-Fraud: Device Restrictions | ||||||||||||||
| Anti-Fraud: Authentication Timeout | ||||||||||||||
| Anti-Fraud: Gender Check | ||||||||||||||
| Anti-Fraud: Age Check | ||||||||||||||
| Anti-Fraud:GPS Check | ||||||||||||||
| Fraud Prevention:LIVENESS | ||||||||||||||
| False Recognition Prevention: Brightness Check | ||||||||||||||
| False Recognition Prevention: Front Facing Only | ||||||||||||||
| False Recognition Prevention: One Person Authentication | ||||||||||||||
| False recognition prevention: Face size check | ||||||||||||||
| Fraud Audit: Retention of facial photo during authentication | ||||||||||||||
| False positive: Third-party authentication | ||||||||||||||
| False positive: Two-step authentication | ||||||||||||||
| Fraud prevention: Role authorization | ||||||||||||||
| Fraud Prevention: Dynamic Scheduling | ||||||||||||||
| Fraud prevention: Authentication scoring | ||||||||||||||
TIGEREYE SECURITY SOLUTION will be standard on all products.
This service allows users to easily prove their identity using only their face, without the need to prepare a card, app or special terminal: simply read the QR code or install a smartphone or tablet to activate facial recognition, which identifies and authenticates the person.
Facial recognition allows for secure and smart attendance management. No card or dedicated terminal is required, and you can easily clock in from your smartphone. As only the person concerned can take the time, there is no need to worry about fraud.
This solution simultaneously checks employee attendance and health by simply recognising their face. Enhanced security, more efficient time and attendance management and improved employee wellbeing.
This product enables login by integrating facial recognition OAuth2.0 into SaaS services. It provides an alternative login format to email addresses and passwords. Facial recognition login eliminates the loss of ID/PW.
Facial recognition is linked to smart keys and electric locks, making it easy to install doors that can be unlocked only by facial recognition. Room access control and unattended room guidance can be achieved without the use of cards or apps.
Facial recognition + blockchain point management system. Facial recognition makes it easy to use points and exchange points with each other without the use of IDs, etc., as logging in is made easier with a 'face'.
This service enables identification at the point of entry to be carried out using facial recognition. As entry is possible with facial recognition, paper tickets are no longer required and there is no need to worry about losing them. There is also no need to scan tickets at the entrance gate. Smooth and quick entry is possible.
Facial recognition ordering simplifies the procedure. Customer preferences can be utilised to improve satisfaction and increase repeat business.
Facial recognition offers advantages such as speedy payment, reliable identification and targeting of campaign information.